ZeroSentinel is a DIY off site privacy node that transforms a Raspberry Pi Zero into a hardened WireGuard gateway and DNSSEC-validated recursive resolver. This guide shows beginners how to build a portable, self-monitoring privacy system that blocks ISP tampering, prevents DNS leaks, and sends encrypted Nostr alerts the moment something breaks. If you want real network privacy without trusting VPN companies or cloud DNS services, this is the blueprint.
You can’t outsource trust. Not to your ISP. Not to a VPN company selling anonymity as a subscription. Not to some app you installed and barely understood. The internet runs on someone else’s incentives. Someone else’s logs. Someone else’s definition of secure.
ZeroSentinel is a small device you build and control. A doorway back into your own network. A resolver that answers to you and no one else. A canary that screams when something breaks instead of leaving you blind. This project is a refusal to trust systems that haven’t earned it.
What ZeroSentinel is
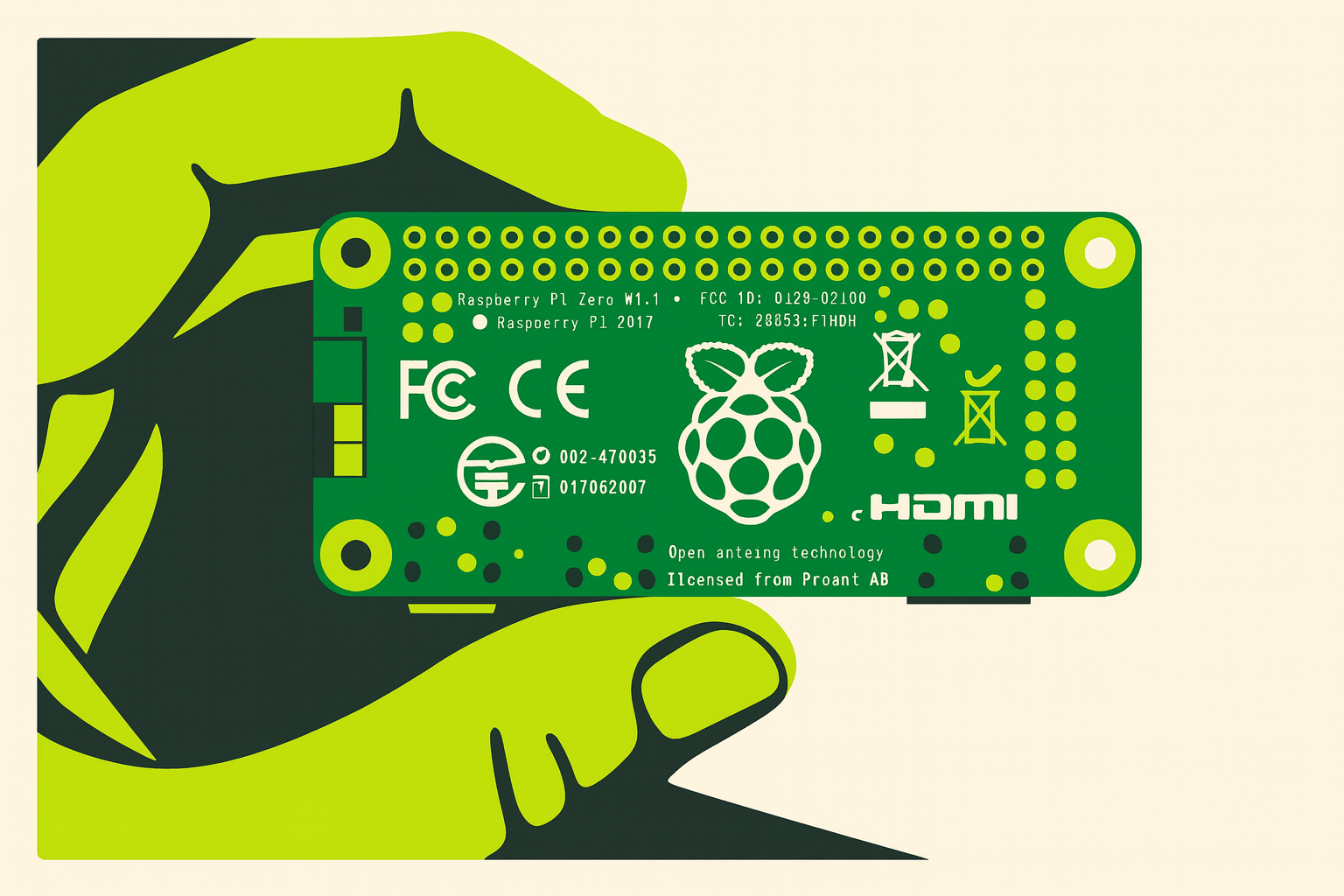
ZeroSentinel is a pocket sized off site access node built on a Raspberry Pi Zero. A tiny computer that becomes your escape hatch on any network you touch. It’s a WireGuard gateway, a DNS firewall, a recursive resolver, and an integrity watchdog wrapped into one tight, portable stack. It sits in your home network or travels with you and gives you a clean, reliable, private path home no matter how hostile the environment is.
And unlike every cloud service you’ve ever been sold, this one doesn’t require faith. You don’t sign up for it. You don’t subscribe to it. You don’t buy trust from someone else. You build and you run it.
What ZeroSentinel does
It turns a small $15 off the shelf device into a fully autonomous privacy node:
- Builds a locked, authenticated WireGuard tunnel home from anywhere
- Runs your DNS through your own Unbound resolver with DNSSEC enforcement
- Cuts ISP tampering, hotel rewrites, captive-portal bullshit, and upstream manipulation
- Monitors its own health every few minutes
- Sends you an encrypted Nostr DM when anything breaks
- Enforces no fallback DNS and drops all traffic that isn’t in the tunnel
- Survives behind travel routers, double-NAT, carrier trash, and hostile networks
- Makes your phone’s “VPN” actually mean something
It’s your own infrastructure, running quietly, checking itself, refusing to be blind.
Explanation for beginners
Here’s the simple version. A Pi Zero is a tiny computer. It’s smaller than a credit card. You plug it into the internet anywhere and it becomes:
- A private connection back to your home network
- Your personal DNS server that doesn’t use corporate resolvers
- It messages you when something breaks
- Your protective bubble on a hostile WiFi
Think of it as a travel safe for your internet traffic. It’s your own infrastructure. It’s a tool that gives you one trustworthy path no matter where you are. And it doesn’t require deep Linux skill to build. I’m going to walk you through that step by step.
ZeroSentinel uses WireGuard. It’s a lightweight VPN protocol that creates an encrypted tunnel between two points. Think of it like running a private cable through the internet. Anything that enters that tunnel is protected, locked, and only delivered to the other end.
DNS is the system that translates human readable names into machine readable number addresses. When you type untraceabledigitaldissident.com into your browser, it doesn’t know where that is. It hands the name to a resolver and the resolver finds the correct IP address so your traffic goes to the right place. DNS is the protocol. The resolver is the worker that carries it out.
Most people use their ISP’s resolver by default or something like NextDNS. Running your own resolver means you control that lookup process instead of handing it to someone else.
The ZeroSentinel has a small script that checks whether your privacy stack is still healthy. Every few minutes it tests the things that matter most like your WireGuard tunnel, your DNS resolver, and your DNSSEC validation. If any of those fail it sends you an alert instead of staying silent. It’s the early warning system that tells you something broke before your device leaks or falls back to an untrusted network path.
Why you want it
- Because relying on someone else’s infrastructure to protect you is a contradiction.
- Because when your tunnel silently drops, your device leaks immediately.
- Because when DNS rewrites happen, profiling comes back instantly.
- Because “secure by default” is just a slogan.
Trust path
Your DNS now belongs to you. Not Cloudflare. Not AT&T. Not a hotel router in the middle of nowhere.
Verification
You get a Nostr DM when:
- WireGuard stops handshaking
- Unbound crashes
- DNSSEC validation breaks
- Upstream dies
- DNS leaks appear
Actual signals.
Portability
Drop it anywhere. Coffee shop. Friend’s house. A sketchy Airbnb. Same tunnel. Same resolver. Same behavior every time.
Predictability
Your traffic goes where you intend. No silent fallbacks. Consistency and control is the real privacy feature.
Control
You stop being a product. You’re running your own infrastructure and system.
Why this matters
Every network you touch wants something from you. Your carrier wants your metadata. Your ISP wants your browsing history. Hotel routers want to rewrite DNS and inject junk and ads. Apps want to phone home. Browsers leak. Phones snitch.
ZeroSentinel doesn’t fix the entire world, but it fixes the part directly under your feet. It gives you a baseline you can trust. A stable home to route back to. A stable thread through a hostile network.
Not perfect. Just better. A lot better.
Limitations and what’s next
A Pi Zero is limited by its processing power and this setup is pushing it to it’s limits. You can create this project on a more powerful board or full size Pi if you’d rather. I chose the Raspberry Pi Zero for it’s low cost, portability, and I had a couple just laying around. This is just Version 01 and a proof of concept of what you can do with a little ingenuity and know how.
This week I will be laying out the build guide step by step:
- The ZeroSentinel Project: Introduction
- The ZeroSentinel Project: Part 1 Setup and WireGuard Install
- The ZeroSentinel Project: Part 2 Resolver
- The ZeroSentinel Project: Part 3 Canary Scripts and Nostr Integration
Refuse the default.
Build your own stack.
Claw it back.
-GHOST
Written by GHOST, creator of the Untraceable Digital Dissident project.
This is part of the Untraceable Digital Dissident series — tactical privacy for creators and rebels.
Explore more privacy tactics at untraceabledigitaldissident.com.
- ZeroSentinel Hub – Your DIY privacy node